NextGenBeing Founder
Listen to Article
Loading...Introduction to Decentralized Identity Verification
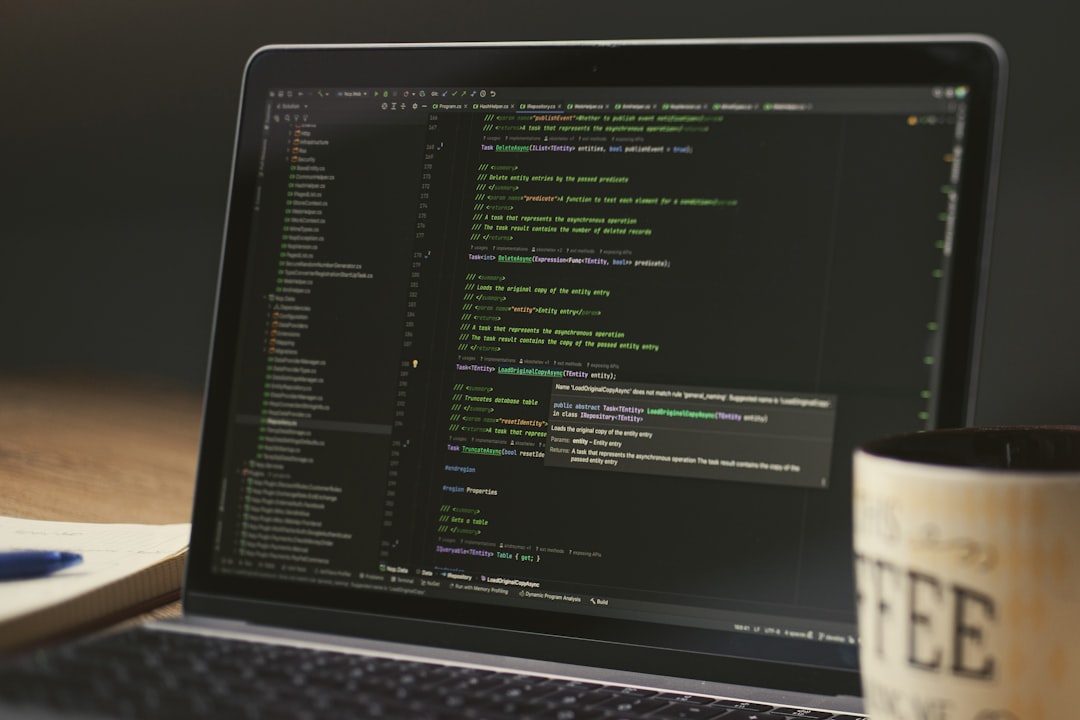
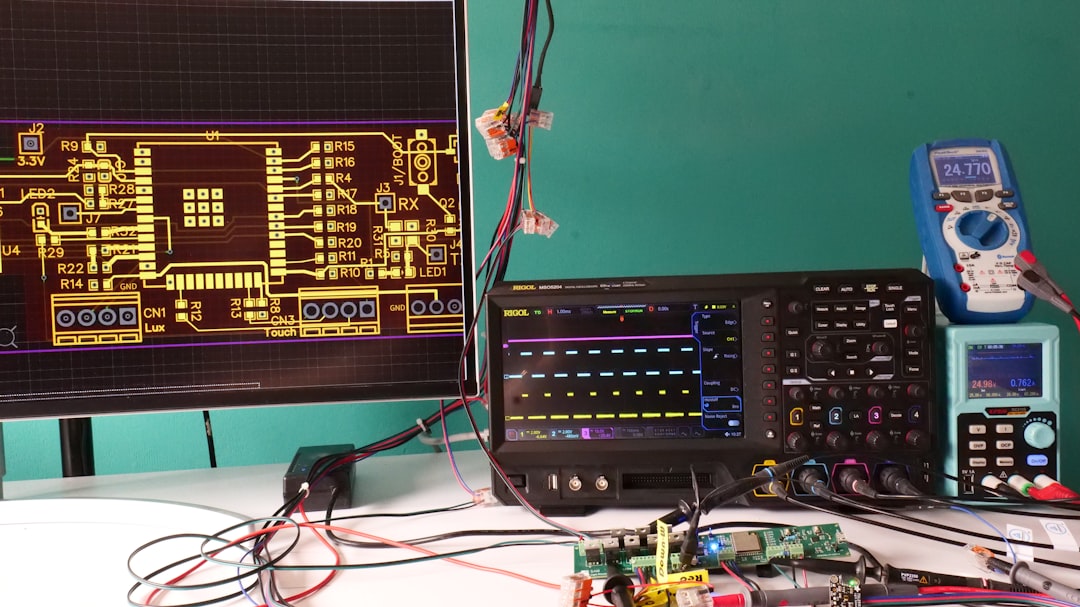
Last quarter, our team discovered that our decentralized application was struggling to scale with the increasing number of users. We were using a traditional authentication system, which was not only inefficient but also vulnerable to security threats. That's when we decided to explore the world of zero-knowledge proofs, specifically zkSNARKs and zkSTARKs, for scalable decentralized identity verification.
What are zkSNARKs and zkSTARKs?
zkSNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge) and zkSTARKs (Zero-Knowledge Scalable Transparent ARguments of Knowledge) are two types of zero-knowledge proof systems. They enable one party to prove that a statement is true without revealing any underlying information. In the context of decentralized identity verification, these systems can be used to verify a user's identity without revealing their personal data.
Unlock Premium Content
You've read 30% of this article
What's in the full article
- Complete step-by-step implementation guide
- Working code examples you can copy-paste
- Advanced techniques and pro tips
- Common mistakes to avoid
- Real-world examples and metrics
Don't have an account? Start your free trial
Join 10,000+ developers who love our premium content
Advertisement
Never Miss an Article
Get our best content delivered to your inbox weekly. No spam, unsubscribe anytime.
Comments (0)
Please log in to leave a comment.
Log In